This is a second post in a series of articles about the SATIE project work-packages (WPs). The idea is to present the reader with more information on the work planned in the project and how planned activities will help to achieve the project goals. This post is about WP3, while future posts will discuss other project WPs.
Aims of WP3
Prevention against cyber and physical threat : This work package is in charge to carry out the technical solutions for the prevention of threat(s) according to different scenarios (both cyber and physical attacks).
Work Plan
This work package is divided into four different tasks in which 13 out of 18 partners of the consortium will be involved.
The first task will be to provide a complete inventory of the airport information system assets by deploying agents or external probe that will be updated in near real-time. Once this inventory available, the system will automatically track and analyze all the cyber-vulnerabilities of those assets via the integration with VIP (Vulnerability Intelligence Platform) and also integration with the tool RIS (Risk Integrated Service). Finally, the goal is to visualize all those vulnerabilities & scoring on a real-time map for airports security officer to monitor any abnormal behavior. Figure 1 presents one of the tools – namely GLPI – used within this task.

Figure 1 – example tool used within WP3 (GLPI)
The second task will be mostly focused the securization of IoT communications on the Baggage Handling System (BHS). To achieve that, the team will design and implement a module/appliance in order to provide authentication, confidentiality and integrity in the communication protocols used, in order to mitigate the risks such as the ones of unauthorized command execution, denial of service, man-in-the-middle and replay attacks. The approach should keep in mind that such kind of module/appliance could be used on other systems of the airport.
The third task will be to reinforce physical access control by combining biometric terminals with video analytic. Biometric terminals alone do present some threat gaps such as tailgating or spoofing attempts. The aim here is to design a solution by adding video analytic & face recognition (via standard IP camera) on restricted access area of the airport. This will increase the resilience to spoofing attempts (by having two modalities verified : fingerprint & face), ensure that only authorized personnel enter the door by preventing tailgating. Finally pro-actively lock the door and send alert to the SOC if an known threat is identified.
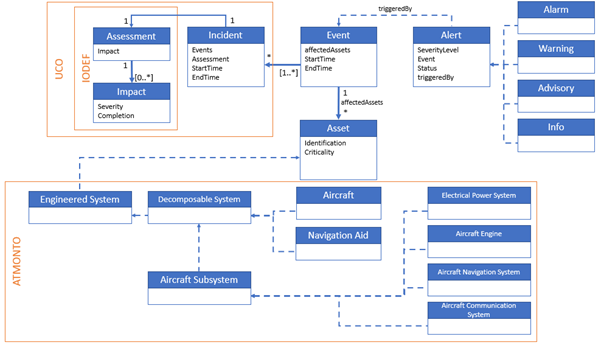
The fourth task is to secure the Air Traffic Management (ATM) of the following data services : FPL Service (Flight Planning Service), NOTAM Service (NOtice To AirMen), MET Service (METeorological data service), PKI (Public Key Infrastructure) & Service Manager. The Secured ATM Services can be made aware of attacks in the physical domain or attempted social engineering to engage reactive security measure. The attacks on the ATM, depending their score on the OSI layer will be detected and managed by SWIM Security & Data Validation (System Wide Information Management)
In order to achieve the goals described above, focus group meetings were planned at each of the three airports with all partners so that the required detailed information about the airports could be collected and person in charge of tasks can start preliminary brainstorming.
In addition, there are bi-weekly web meetings with the relevant partners to ensure regular communication and updates, resolving any issues that arise, and verifying that the tasks stay on track and on schedule.
To ensure high-quality work, partners have been included which have specific expertise with risk analysis, propagation modeling, and management strategies. Having the one united goal of improving cyber-physical security in airports ensures that all partners work together in a collaborative and cooperative manner.
Note: This output reflects the views only of the author(s), and the European Union cannot be held responsible for any use which may be made of the information contained therein. This project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement No 832969.